Dawn broke. With a deep breath, I analyzed the the thick morning air. I sampled its nuances, sensing the fear. Wildlife everywhere trembled in anticipation of the hunt to come. I rose, eager for the stalk.
I’d like to say that’s how the day began, but I’ve never been a morning person. When I was a child, it was my sister who woke me for Saturday morning cartoons. High school fared no better, as evening extracurricular activities intruded upon homework and leisure time, and in turn brought about a later bed time, which naturally led to morning routine difficulties. In college, I worked after class, often closing the department at 10PM. After college, I worked second shift for years. It is only recently that I began working normal hours, but the actions of a lifetime have driven deep habitual behavior, and I find my body very unwilling to change its customs now.
Instead, the alarm went off at my usual 6AM, whereupon I followed a standard routine to deliver the kid to school. Then, after brewing a pot of coffee and loading the hunting gear into dad’s car, the ruthless caveman hunters that we were began our journey in the comforts of a climate controlled sedan. I admit–modern hunting is definitely a privileged man’s sport, a far cry from its beginnings as a survival activity, and certainly a pretty pathetic claim at representing the planet’s apex predator.
Our destination was the Clark Lake Wilderness Area. In years prior, we had struggled to find bountiful hunting grounds, and out of sheer chance, I had discovered this little alcove. It was obviously set aside for one purpose–hunting. It’s very design made this implication clear, having landscaping engineered to match the natural habitat of indigenous prey. But more importantly, it was the only place we had tried in this region that had netted results. So it was an easy decision to make.
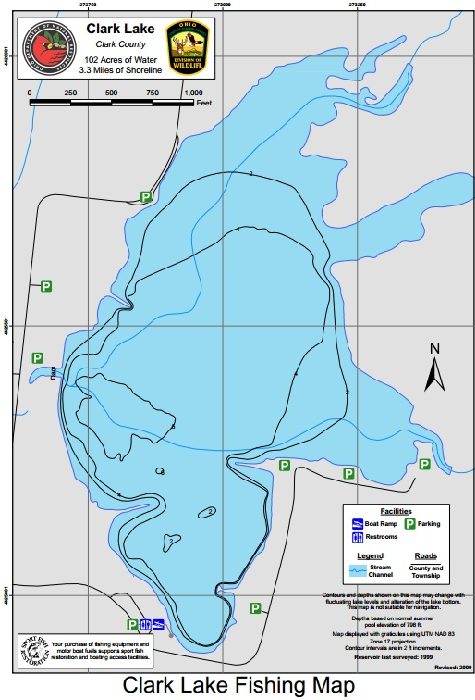
The road terminates in a parking lot on the eastern side of the lake, and this is where the large wooded lot resides. However, if you look on the map above, the parking lot just west of that is in a clearing, and in that clearing is an isolated grouping of 3 trees. The last time we hunted here, on the way out of the woods, with no kill to our bag yet, I saw squirrels in those trees. At the time, I had yelled at dad to stop the car, and I leapt from it (while it was still moving) with my 20 gauge and ran across the clearing to get in range. I managed to drop two squirrels with my single shot shotgun. So this time, as we made our way back upon the old road, dad joked about that time prior, and suggested we check there first.
He immediately spotted 3 squirrels. I, being unsurprisingly less agile than I was in years past, methodically laced my boots and donned my gear, figuring squirrels generally pay no heed to humans. Of course, this false assumption was based upon my interactions with suburban squirrels. By the time I was ready, these squirrels had vacated, save one, who scampered up a tree and hid. So we waited.
Eventually, as we were giving up, I saw a flick of the tail. Perhaps it was the extensive time I’ve had with that one weapon, or perhaps it was a trained muscle reflex, or indeed it was my ruthless predatory instincts, or all of the above; but I immediately dropped the squirrel with a single shot.
But the shot had missed the brain stem. The unfortunate creature twitched for a time, until dad finished it off with his knife. I winced as he pithed it. But part of why I hunt is to remind myself what’s behind the meat we so readily buy. There’s always a cost in suffering, and taking a personal hands-on approach drives this point home.
Moving on, we followed a deer trail, it was my turn to jest about a second particular tree that had yielded a squirrel last time. Moments later, a red squirrel began running down that very tree. I fired as he hit a patch of twigs, so I didn’t see the impact, but he fell into the mired jungle behind, and I got thoroughly soaked from the knees down trying to retrieve him from the brush. The week’s rain and the evening dew had saturated the undergrowth. But, two squirrels we now had.

We continued to the main wooded lot and split up. I note dad chose the easier path, whilst I got the jungle. Between the blackberries, the garden spiders, the water, the humidity, and the rising temperature; I found the experience trying (I later referred to it as a Vietnam simulator, to which dad thought I was being overly-dramatic). I did see another red squirrel, and I fired, but I was bogged down at the time and just slightly too slow. He got to see another day.
Not long after, I heard a shot, and presumed correctly that dad had bagged a squirrel of his own. I knew from experience that he moves painfully slow through the woods, but when I tried to slow my own pace, I discovered a cloud of mosquitoes had identified me as a mobile buffet. Then I ran into another couple hunters, so there was just too much movement to hope to find anything else. I tried to find dad.
Yet dad, despite the orange vest, always proves elusive, and I had to resort to modern technology. But it’s not every day that someone sends a text to rendezvous at the dry stream bed. Here’s another reason I hunt–the joy of practicing land navigation skills. Whilst traversing wilderness, it behooves the adventurer to remember enough features so as to find the way back (sans-smartphone). Thankfully, I’m still good enough at it that I knew immediately where he was. And sure enough, he had a squirrel. One’s a success, three’s a bounty. Dirty and sweaty, we left for home.
And I’ll note that dad jumped in the shower right away, leaving me to do the cleaning. But like the killing, it serves as a reminder. Eating meat is a privilege, and requires a lot of unpleasantness first.

Squirrel reminds me of a really mild pork, and as woodland squirrels subsist on nuts and fruit, are probably of a much higher quality than anything store-bought.
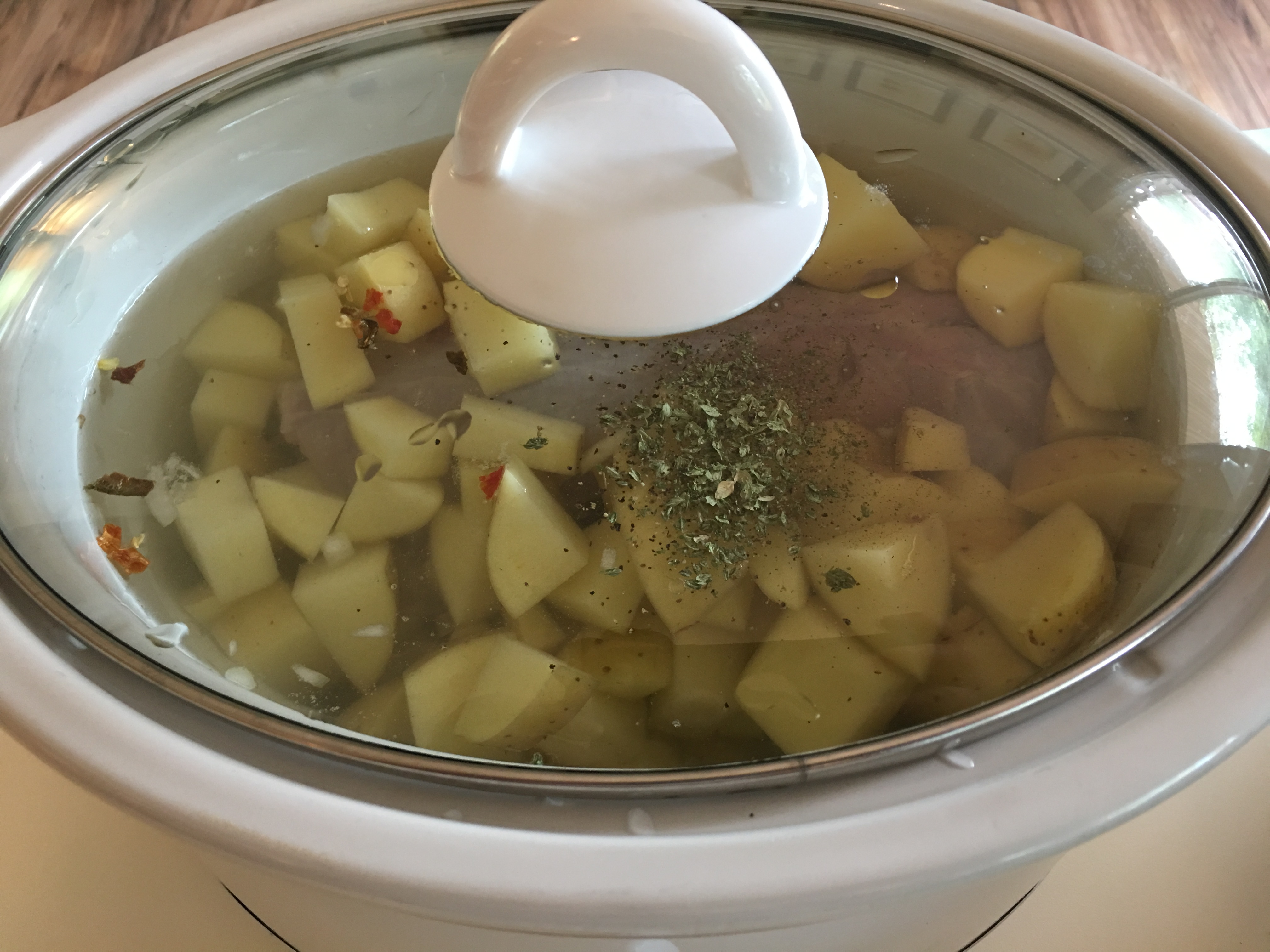
A few hours in the crockpot yielded a tasty stew. Even the kid ate it. Liz–not so much. Her culinary curiosities apparently have their limits, and eating tree-rat was beyond them.
Some celebratory bourbon and the old man was out. Each time we hunt, I tell him when he’s old and useless I’ll just shoot him in the woods. But I think the kid still needs her grandpa, so I’ll keep him around a little longer. That, and then who would I go hunting with?
Next up, it’s wabbit season.
–Simon


